Over the weekend I ran into a weird issue that I hadn’t seen before. I was upgrading half of the Distribution Points for a client who’s ConfigMgr was in need of some TLC. I’ve been working on getting their overall infrastructure healthy and that includes upgrading their DPs from Windows Server 2012 to Windows Server 2016 (and eventually 2019).
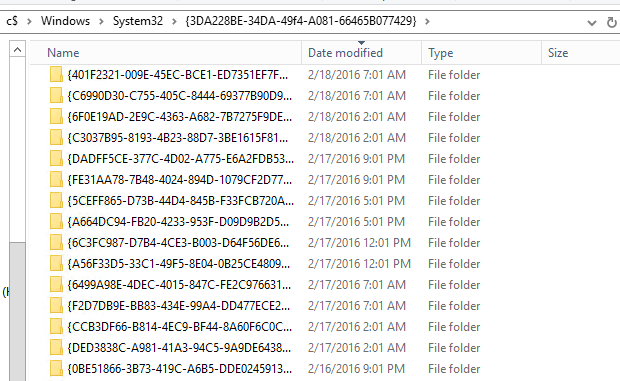
Once I started the upgrades I worked on other things while checking in on them periodically. After a few hours I discovered that they were all still offline and I could only access them via the C$ admin share (C**-Money** as Ben Reader calls it). I checked the setupact.log and found that each server was stuck doing the same thing - recursively migrating folders from the old OS C:\Windows.old\Windows\System32\{3DA228BE-34DA-49f4-A081-66465B077429} to the new OS C:\Windows\System32\{3DA228BE-34DA-49f4-A081-66465B077429}.
C:\Windows\System32{3DA228BE-34DA-49f4-A081-66465B077429}
After over 12 hours of waiting for setup to complete, my contact at the client company rebooted the servers in VMWare and the servers rolled back to Server 2012. After deleting the folder contents, the upgrades all completed fine.
During this process, I checked all of the hung servers and found that the each had 60,000-100,000+ {GUID} folders, each with a sub folder called badmifs. ConfigMgr uses mif files (I thought mif meant - Machine Inventory File, but according to Garth, it means Management Information File. Garth knows everything.) so I at least had a starting point for finding the source of the folders. The issue here was that the migration process was crawling - copying 1 folder every 2 seconds with an expected completion of sometime next Tuesday! After remotely running rmdir /q/s for several hours on several of them, which was working, just slowly, I realized that I could just relocate the entire folder to the root of c:\ in a few seconds and delete them after the upgrade was complete, which is what I did using the aptly named move command.
This morning, I reached out the the ConfigMgr team to file a bug and already heard back that they found the source and ultimately that this folder is linked to some legacy code and can safely be deleted (Thank you for the help on this!!).
Even though this will likely be fixed in a future release, I was curious about the source still. After searching all through the registry, started checking the client install logs the log I was looking for. It confirmed that the root folder C:\Windows\System32\{3DA228BE-34DA-49f4-A081-66465B077429} is created as a backup folder by the ConfigMgr installer client.msi where it’s backing up old settings/inventory data to a new {GUID} folder before upgrading the client, then it restores the data back, but seems to be leaving the backup folders behind. Check out this excerpt from C:\Windows\ccmsetup\Logs`client.msi.log` file from one of my production workstations.
| |
In my client’s environment, the number of folders seemed to be quite excessive so I checked my production environment to compare by using Run Scripts to run a small PowerShell script to output the count of folders found (see below for code). I found that on average, my machines have about empty 24 folders in this location with the largest number hitting ~600 folders. When I checked the workstation with ~600 folders, I found that a majority of them were created on the same day and had the same timestamp which feels like it could be caused by a client install that is failing in some catastrophic way - just a guess though. I also did the same check in my client’s environment and found that there may have been a client health service that was attempting a repair every 5 hours, ever day, FOREVER!
Ultimately, I was instructed that the folders weren’t needed and could be safely deleted. So I updated my discovery script to check for the folders and delete them where necessary. Since the deletion of a large number of folders was taking hours, I tested out using robocopy with the /mir command to copy over a blank folder and overwrite the existing folder. This improved performance drastically! My lab is giving me issues tonight, but I will try to get the script added to the ConfigMgr Community Hub for easier downloading. In the meantime, I’ve included a link to the script in my Github repo as well as included it below.
I should mention, I am not concerned about a small number of folders, even a few thousand likely won’t slow down an OS upgrade enough to worry about. This is about ensuring that we don’t have other machines hang during upgrades as we roll out Windows 10 Feature Updates and other servers are upgraded.
⚠️ CAUTION - This script can wipe out folders if used incorrectly. Proceed with great care and test before running it.
| |
Summary
This was a very interesting challenge that let me learn several new things.
- Items within
C:\Windowswill migrate during a Feature Update or OS Upgrade as long as they aren’t in default locations that are excluded by the default migration mapping engine. I had previously thought this wasn’t the case. It means I may be able to move my feature update scripts into a more secure location. - Robocopy is faster than other file/folder deletion options. The included script can easily be re-used to rapidly clear out large folder structures
- The ConfigMgr client has a storied history and still holds many secrets 🙂
Special thanks to the some of folks over at the WinAdmins Discordserver who helped me validate my findings and the ConfigMgr team taking a look at the issue so quickly.
Adam Gross Founder
Adam is a Microsoft MVP in Enterprise Mobility and is the founder of SysManSquad